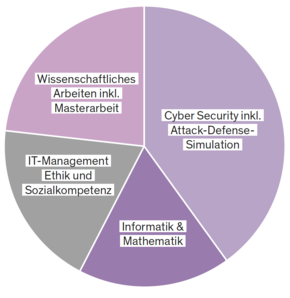
The programme is based on an engineering-based education and includes network and security technology, IT, mathematics and ethical aspects. You will also acquire entrepreneurial and social-communicative skills.
We place particular emphasis on the following three key areas during the course:
- Operations Security
- Attack defense simulation
- Human attack vector
Focus areas

Operations Security
Whether a small company or a large corporation - a functioning IT and network infrastructure is essential for smooth day-to-day operations. The course therefore focuses on the design, commissioning and maintenance of such infrastructures. You will acquire the skills to realistically plan and securely operate small and large networks as well as a wide range of IT services and servers. After completing this degree, you will also be able to continuously check existing infrastructures for potential weak points and secure them using state-of-the-art technology. These practical skills are based on theoretical specialist knowledge at Master's level - particularly in the areas of security, networking and privacy. The optimal combination of theory and practice opens up career opportunities in various areas of operational IT security, from small companies to large corporations.

Attack-Defense-Simulation
At the heart of the training is the central attack-defense simulation, which is intensively supervised in small groups and in which you will be confronted with a wide variety of attack and defense situations over the course of two semesters. You will learn how to prepare for these and receive structured feedback on your behavior under time pressure and other stress factors in order to be even better prepared for future situations. In combination with the technical content taught in the course and the social and communication skills practiced, the attack defense simulation enables realistic preparation for real cyber attacks in the corporate environment, where such skills are in high demand.
Human attack vector
In addition to technical vulnerabilities, humans are one of the biggest targets for cyber attacks. Through clever manipulation, such as disinformation campaigns or phishing attacks, criminals or state actors try to obtain targeted information and data or influence the behavior of certain groups. This is why you will deal with the topic of social engineering. You will receive a psychologically sound introduction to human behavior in the context of security. In this way, you can not only strengthen IT security with the help of technical defensive measures, but also further increase it by raising awareness and taking organizational precautions.
